
Cyber Security
This service is for teams that need confidence in how their application, website or server behaves under real usage and adversarial thinking.
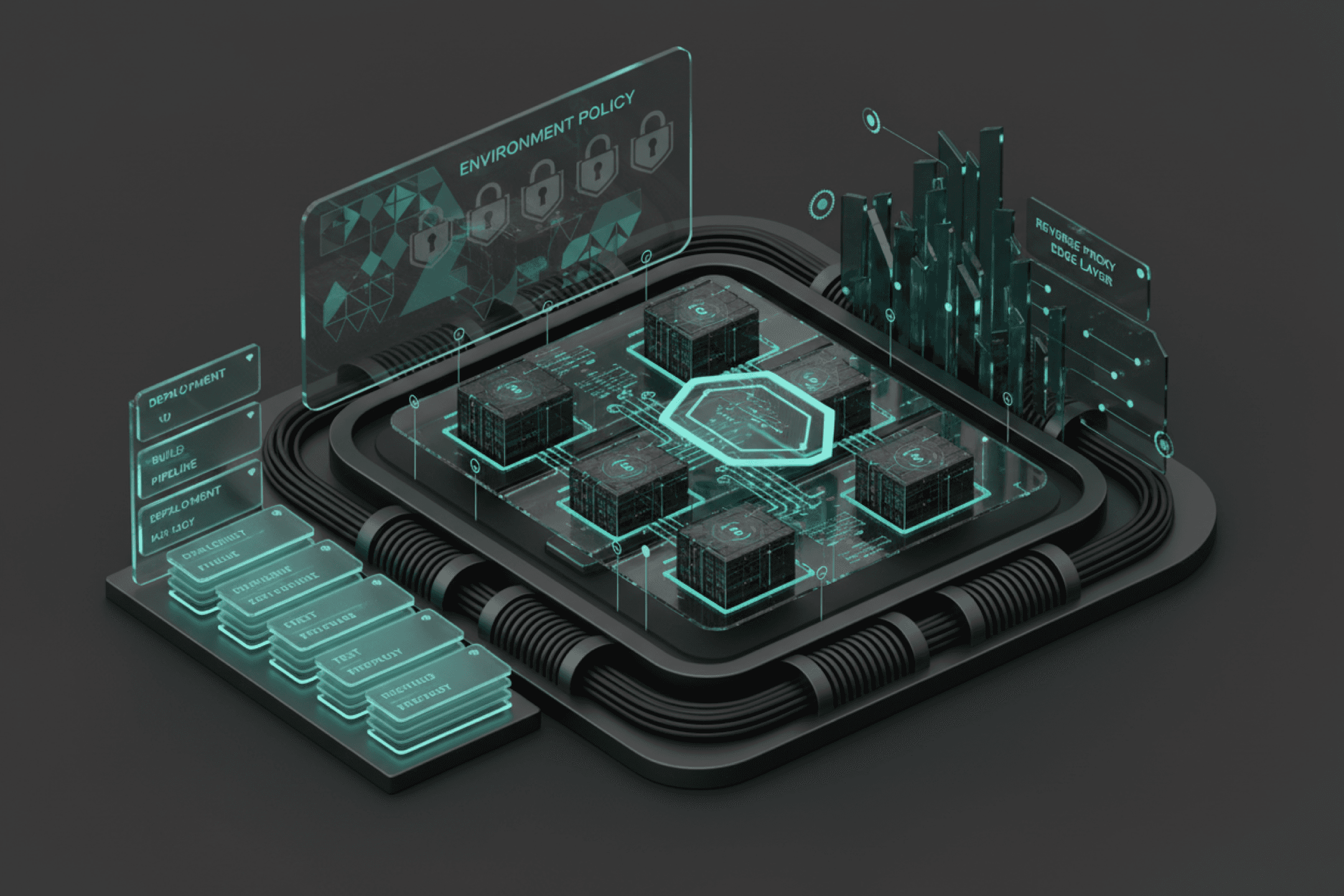
I review the parts of the stack most likely to create security debt: auth boundaries, session handling, risky flows, exposed admin surfaces, third-party assumptions and missing operational controls.
Delivery focus
- • Application and runtime review
- • Authentication and permission analysis
- • Prioritized hardening guidance
Primary goal
Capabilities
Cyber Security
Practical security reviews and hardening for authentication, permissions, attack surface and runtime exposure.
Risk map
A practical summary of the highest-priority issues and trust gaps.
Flow analysis
Auth and request lifecycle review with concrete notes on abuse paths.
Remediation plan
A sequenced fix plan aligned with business urgency and delivery capacity.
View service
Surface the sensitive flows
Understand where identity, privileges, data handling and third-party trust boundaries intersect.
Challenge the implementation
Review assumptions in code, routing, headers, session logic and runtime behavior.
Turn findings into action
Package the output into fixes the product team can actually prioritize and ship.
Primary goal
Delivery focus
Project brief
Related projects
Related projects
Practical security reviews and hardening for authentication, permissions, attack surface and runtime exposure.

2026
Threat Surface Portal
An internal portal to unify visibility across domains, issues and externally exposed systems.
2025
Coolify Secure Runtime Baseline
A hardened deployment baseline for self-hosted workloads combining lean images, security headers and operational clarity.